
In today’s world, data breaches are becoming more common and sophisticated. Keep your data safe by planning today for inevitable attacks tomorrow.
Here's how SynerComm's CASM solution is different:
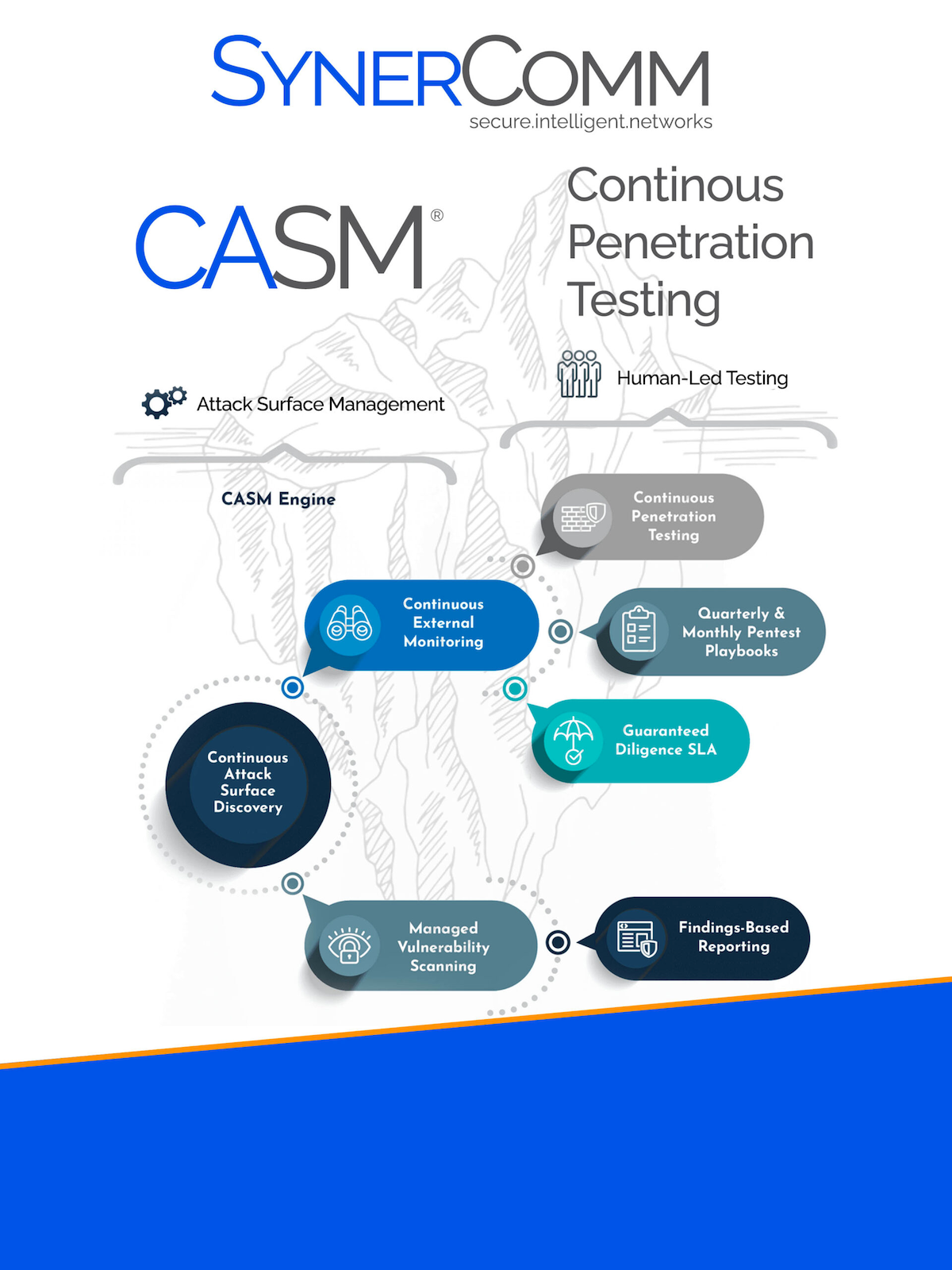
For even more protection, you can choose to pair CASM’s 24/7 monitoring with Synercomm's best-in-class penetration testing to achieve Continuous Penetration Testing.
To define CASM, we should first agree on what we mean by an “attack surface”. In its broadest meaning, it’s everything that could create or allow risk to an organization. Continuous Attack Surface Management, or CASM, is all about orchestrating and automating numerous critical security processes to significantly reduce the time to detect and respond to risks.
To be effective, a CASM solution must automatically discover assets, intelligently assess risks, remain accurate and up-to-date, and reduce or eliminate the human effort needed to measure and report risk. SynerComm’s CASM® platform is a SaaS solution providing complete external risk and vulnerability management. Designed by penetration testers, CASM provides security professionals, risk managers, and auditors with a complete and accurate view of your assets and risks.
CASM was designed to be autonomous to free you up for other important business. Our automatic discovery will find and start monitoring new servers/services throughout the internet, including the cloud! A vulnerability creates risk until it is corrected or removed. CASM alerts you to vulnerabilities so they can be mitigated before hackers can find them.
Not only does CASM automatically discover your internet-connected assets, but it also provides an always up-to-date asset inventory we refer to as your attack surface. You may not have hired additional staff, but it feels like it when you subscribe to CASM. Our CASM Engine® scanners were built by penetration testers to “automate everything safe to automate”.
CASM also integrates with most popular cloud providers like Amazon Web Services, Microsoft Azure and Google Cloud. Our APIs allow you to integrate into nearly any process or application. With fully customizable alerts and notifications, you decide what’s important. Be sure to check out CASM’s new Slack channel notifications!
The best candidates for CASM are organizations that are challenged with keeping up with the volume, volatility, or regional distribution of their assets.
Organizations with 10 to 10,000+ external (internet-facing) assets or a high degree of external system changes would be prime candidates for CASM. Additionally, organizations migrating to the cloud or those looking to automate their external discovery and vulnerability management would greatly benefit.
Continuous vulnerability management describes ongoing monitoring, testing, remediation, testing, etc. for vulnerabilities. The Center for Internet Security CIS Critical Security Controls lists Continuous Vulnerability Management as their #7 control.
CASM is the fastest and easiest solution for companies looking to achieve continuous (external) vulnerability management. CASM at its most basic level does not perform vulnerability scanning. As such it is faster and less intrusive and it does not provide potential vulnerability findings.
Yes. CASM fits into most frameworks' requirements for inventory, change detection, and risk review processes. It was designed to be agnostic and to support all popular standards.
Dashboard – CASM is a SaaS platform accessible by any modern web browser. In addition to viewing data and running/downloading reports, the CASM dashboard is used for administration.
Monthly – PDF attack surface reports can be delivered automatically or downloaded through the dashboard.
Findings – Findings are CASM’s most important notifications. CASM subscribers are alerted when a new finding needs attention.
API Integration – Not all roles require web-browser-based access to information. CASM’s APIs allow you to integrate into nearly any process or application, including Slack and ServiceNow.
Most CASM subscribers are up and running in less than 15 minutes.
The actual resources needed are often determined by how well our clients know their systems.
This first step is referred to as “scoping” and CASM was designed to make it as painless as possible. Using our automated asset discovery, your team merely confirms or excludes systems from being monitored and tested. After that, CASM runs autonomously and is always ready when you need it.
Some roles benefit from regular research and monitoring of assets through CASM while others are completely hands-off unless they are responding to a finding.
Start a free 14-day trial today! | Contact us