Continuous Penetration Testing (CPT)
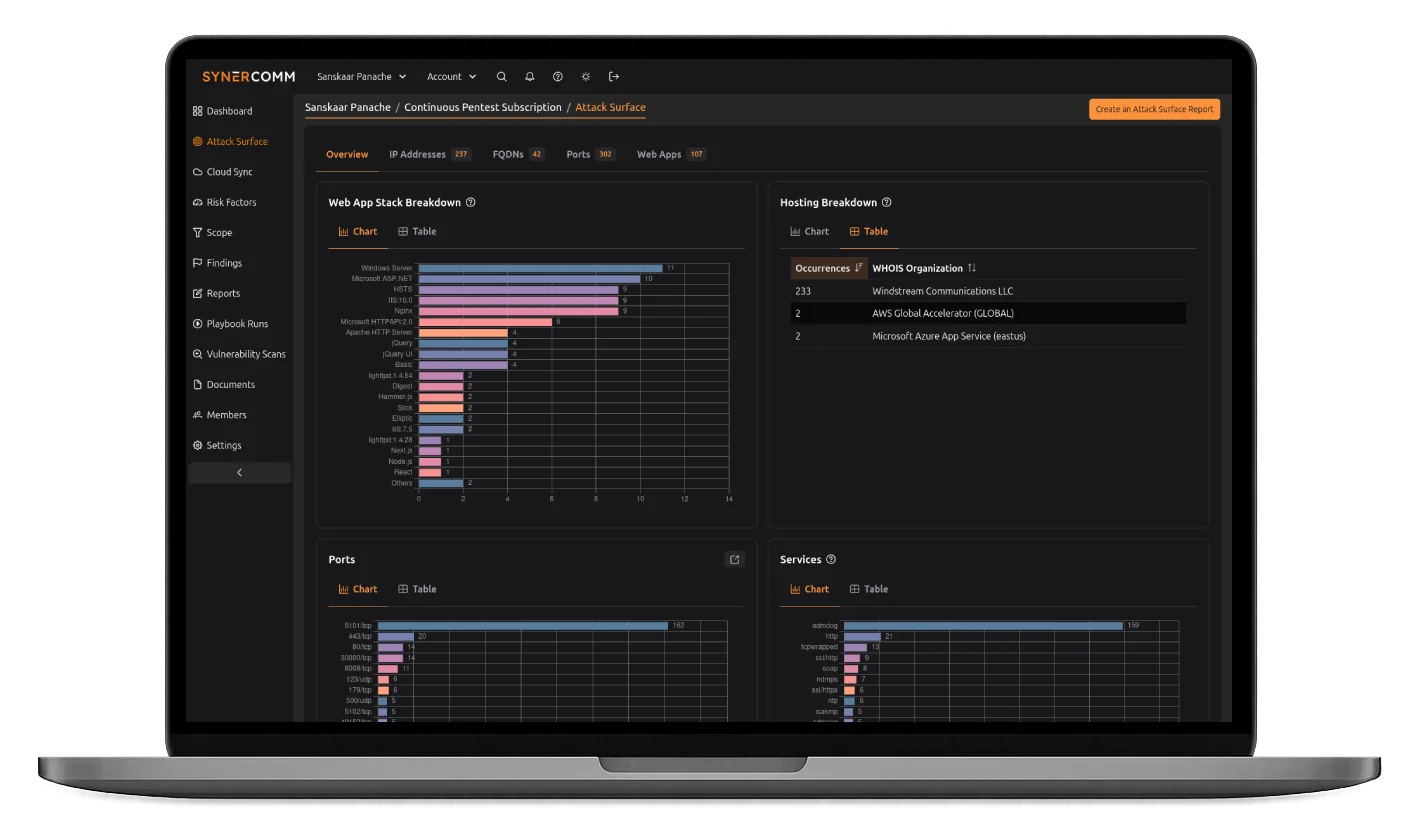
Powered by CASM®
Regular penetration testing is essential, but it’s only a snapshot in time. Continuous Penetration Testing builds on that foundation, delivering year-round threat coverage, faster detection, and complete protection against evolving vulnerabilities and attack techniques.
Continuous Protection for Your Evolving Environment
Whether you’re securing cloud environments, deploying new applications, or managing compliance requirements, continuous penetration testing provides the year-round assurance modern organizations need. While threats never stop evolving, neither does our protection. Transform your security strategy from periodic checkups to continuous vigilance. Let’s strengthen your security posture together.
A point-in-time penetration test shows you where your security stands today, but what happens tomorrow?
If attackers are active 365 days a year, shouldn’t your pentest do the same?
As you explore security solutions, you’ll encounter a confusing array of terms: Penetration Testing as a Service (PTaaS), Continuous Threat Exposure Management (CTEM), and Attack Surface Management (ASM).
Rather than layering multiple services, we combine these concepts into one comprehensive solution, blending automation with human expertise for continuous protection.
No matter what you call it, the outcome is the same: Fewer blind spots. Faster detection. Stronger security year-round.

Why Annual Testing Falls Short
Traditional penetration testing leaves a dangerous gap between assessments. Consider what happens during those intervals:
New vulnerabilities
go unnoticed for months.
Network changes
Attackers gain time
How Continuous Penetration Testing Keeps You Protected
24/7/365 Attack Surface Monitoring
CASM continuously tracks your environment, discovering new assets and identifying risks as they emerge, so you’re never caught off guard.
Pentester-Validated Findings
Every finding is created by expert penetration testers, ensuring you’re only alerted to verified risks, no wasted time chasing false positives.
On-Demand Testing for Immediate Coverage
When you add new applications, change configurations, or deploy new services, CPT ensures those changes are assessed without delay.
Unlimited Retesting for Confident Fixes
We don’t just flag vulnerabilities, we confirm they’ve been fixed, giving you peace of mind that remediation efforts are effective.
Actionable Reporting That Drives Results
Our reports cut through the noise, delivering clear insights and prioritized guidance so your team can focus on what matters most.
A Team That Becomes Your Team
With CPT, our penetration testers become an extension of your security team, available to assess new risks and answer your toughest security questions.
Playbooks That Adapt to Emerging Threats
Your security posture evolves as fast as attackers do.
At the heart of our approach are specialized playbooks that evolve with the threat landscape. These proven methodologies ensure consistent, comprehensive protection:
Recurring Playbooks focus on routine tests and common risks like password spraying, MFA bypasses, and information disclosures; the security gaps that require frequent attention.
Emergency Playbooks provide rapid response to late-breaking vulnerabilities often tied to new CVEs or active exploit campaigns.
Beyond Vulnerabilities: Identifying Systemic Issues
Finding vulnerabilities is important, but identifying why they keep happening is the key to improving security.
With an ongoing CPT engagement, our testers identify:
Recurring weaknesses that expose larger security gaps.
Patterns that point to deeper flaws in processes, configurations, or systems.
Root causes that help you break the cycle of repeat vulnerabilities.
Turn your security team from reactive to proactive, ready to stop threats before damage occurs.

Cybersecurity
Services
CHALLENGE
Drowning in Noise, Missing Real Threats?
Constant alerts make it hard to prioritize real risks, draining resources and leaving your business exposed.
SOLUTION
With continuous penetration testing and CASM® for real-time attack surface management, we cut through the noise to spotlight the threats that matter most.
OUTCOME
Confidently prevent breaches by focusing on real threats.

Infrastructure
& Network Services
CHALLENGE
Scaling Networks, Stagnating Security?
Growing businesses often face network bottlenecks and security gaps.
SOLUTION
Our Digital Twin Lab simulates and validates network changes. Our A-Team designs secure, adaptive networks that scale with your business.
OUTCOME
Technology
Optimization
CHALLENGE
Tech Stack Chaos Draining Resources?
Redundant tools and inefficient systems drive up costs and slow down operations.
SOLUTION
Our A-Team optimizes your tech environment, eliminating redundancies and ensuring seamless integration.
OUTCOME
Reduce costs and boost efficiency with a streamlined, high-performing tech stack.
