Blog
Insights From Cybersecurity Experts

The Business Case for Purple Team Exercises
Most security programs spend millions on tools and people, then rely on dashboards and assumptions to tell them everything is working. Purple team exercises close that loop. A purple team...
How to Evaluate Penetration Testing Services Effectively (A Buyer’s Guide)
How to Evaluate Penetration Testing Services Effectively (A Buyer’s Guide) Penetration testing services can be one of the highest-ROI security investments an organization makes, if the right...
AI Adoption Is Accelerating: How to Prove Your Governance and Controls Actually Work
AI Adoption Is Accelerating: How to Prove Your Governance and Controls Actually Work Practical validation through adversary-informed testing and configuration alignment AI is no longer experimental....

How to Assess Active Directory Passwords and Hashes: Hash Master 1000 v2.0
Turning Password Data into Meaningful Insight Our consultants often spend time helping organizations better understand concerning truths about their environments. Password hygiene continues to be a...

CMMC Level 2 at Enterprise Scale
CMMC Level 2 at Enterprise Scale: Why Programs Stall and How to Get Unstuck CMMC Level 2 readiness is no longer theoretical. For large enterprises, especially manufacturers with complex IT and OT...

DNS Security: The Internet’s Most Critical and Most Overlooked Attack Surface
DNS is foundational to availability and trust, yet often under-protected. Discover key DNS attack vectors, modern threats, and how CISOs can implement layered DNS security.

When “Malicious” NTP Traffic Isn’t Malicious at All: Understanding False Positives from pool.ntp.org
Security teams rely heavily on reputation-based threat intelligence to block malicious traffic. These controls are effective at shutting down known command-and-control servers, botnet servers, Tor...

Healthcare Domains : The Prescription for Bypassing SSL Inspection
Next-gen firewalls with SSL inspection are one of the strongest defenses enterprises deploy to detect malicious traffic like command-and-control (C2). By decrypting and inspecting encrypted...
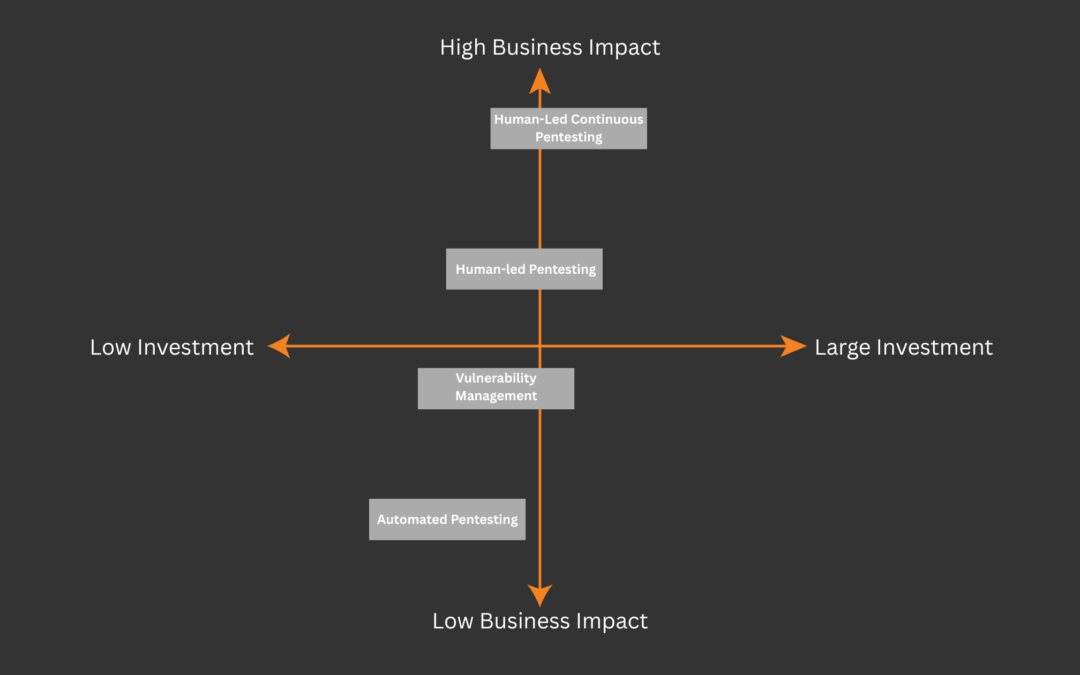
Beyond the Checkboxes: Increasing Value & Reducing Risk
Part 2: Why Continuous Penetration Testing is a “No-Brainer” Investment Ever wondered whether you’re getting everything you can from your penetration testing program, you’re not alone....
Beyond the Checkboxes: How Continuous Testing Reveals What Others Miss
How continuous penetration testing reveals vulnerabilities that others miss through expert penetration testers, mature processes, a robust platform, and long-term partnership: continuous penetration testing reveals vulnerabilities that others miss.
Does this SOC fit?
A look into what the SOC process was designed for and how to determine if it is something you need.

Beyond the Slide Deck: Modern Tabletop Exercises That Prepare You for the Real Thing
For years, tabletop exercises (TTXs) have been a go-to method for testing an organization’s cybersecurity response plan. But as cyber threats evolve and real-world attacks grow more complex, so too...

The #1 Defense Against Business Disruption & Financial Loss from Cyber Threats
Your organization has invested millions in cybersecurity tools. You've deployed next-generation firewalls, implemented endpoint protection, and built a Security Operations Center. Your compliance...
How CASM® Works: Part 1 – Asset Discovery with ML
A semi-technical look at how CASM, the platform powering Continuous Penetration Testing, uses machine learning to discover attack surface assets.

IT Infrastructure Modernization: Hidden Costs and Strategic Risks
Legacy IT infrastructure represents one of the most significant yet understated risks to modern business operations. While these aging systems continue functioning day-to-day, they're silently...
