Blog
Insights From Cybersecurity Experts

Incorporating Your Lessons Learned for Pandemic Contingency Planning Considerations
Although contingency planning has a healthy focus on technology, it still requires people to interface with that technology, configure and program the technology so that it will perform some...
We’ll get through this; how will it make us stronger? Make COVID-19 “lessons learned” a priority
The COVID-19 event, obviously, has had a wide-reaching negative impact for the entire country. Despite this, even in the face of the trauma linked to the loss of loved ones, we will eventually...

Continuous Penetration Testing
“So, let’s say we fix all of the vulnerabilities that the pentest discovers… How do we know tomorrow that we’re not vulnerable to something new?” ~Customer Bridging the Gap Between...

People are People, but Where Can You Find Them When You Need Them?
Trying to find qualified IT infrastructure and security people? We at SynerComm help companies successfully overcome that challenge every day, and so I suppose I suffer from the old adage: “to a...
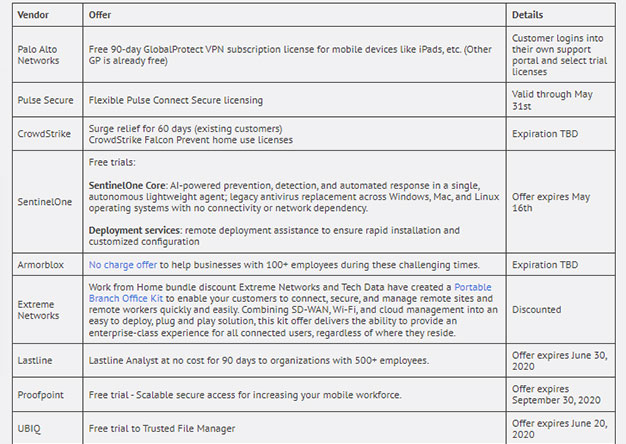
Vendors Stepping Up in a Time of Need
Most enterprises are getting slammed with employees working from home. Most of us designed our remote user VPN’s for the occasional "snow day" ...right. Now we have an entire workforce, working from...
Remote Access Rush
Practicing good remote access hygiene in times of uncertainty As the business world reacts to the current health crisis, companies are offering remote access to any role that can work from home....
Are we prepared?
Risks and Considerations for IT: A Pandemic What can IT do to prepare? We all know the stats of the Coronavirus, although they are changing by the minute. We know what to do personally and for our...
Cybersecurity Maturity Model Certification (CMMC)
From a quick assessment on what has been published thus far on the CMMC regulation and its overall goal, it appears that contractors lack of information security will no longer be tolerated by the...
Understanding HIPAA: PHI and Covered Entities
Medical community challenge: In a business environment where resources are limited, compliance requirements abound, and budgets are constantly challenged to meet cost containment targets, the...
Understanding HIPAA: Starting with the Rules
Medical community challenge: In a business environment where resources are limited, compliance requirements abound, and budgets are constantly struggling to meet cost containment targets, the...
Why Microsoft Office 365 Secure Score Isn’t Enough
Microsoft Secure Score. If you’re an IT administrator or security professional in an organization that uses Office 365, then you’ve no doubt used the tool or at least heard the term. It started as...
How to Approach the General Data Protection Regulation (GDPR) With a Security Framework
GDPR has been in place since May 25th, 2018 and has already been used in legal actions against companies, with over 200,000 cases reported within this first year. The law is expected to make a...
Framework or Crash, the Choice is Yours!
Are you using a framework to establish your information security program? If not, I get it; it’s complicated. On a second thought, have you lost your mind? I’ve been there. A number of years ago,...
Lessons Learned from Pentesting – What Should Keep You Up At Night
Coming from someone who can officially say that information security has given me a few gray hairs, I'm writing this article from the perspective of someone who's been around the block. With over 15...
Characteristics of a Relevant Information Security Program: Communications
The Challenge You budget for, enable, and staff your organization’s information security program with people, technology, and visionary prowess. As you step back and observe do you find yourself...
