How to Evaluate Penetration Testing Services Effectively (A Buyer’s Guide)
Penetration testing services can be one of the highest-ROI security investments an organization makes, if the right provider and scope are selected. The challenge is that many penetration testing firms market similar promises while delivering very different levels of depth, realism, and follow-through.
This guide explains how to evaluate penetration testing vendors, how penetration testing differs from vulnerability assessment services, what strong deliverables look like, and which questions buyers should ask before signing a statement of work. It also highlights common pitfalls and provides a practical scorecard to support vendor selection.
Understanding Penetration Testing vs. Vulnerability Assessment Services
Vulnerability assessment services are designed to identify potential weaknesses, often at scale, by scanning systems, enumerating software versions, and mapping known issues to CVEs. They help answer the question, “What might be wrong?”
Penetration testing is designed to validate exploitability and impact by behaving like a real attacker. This includes chaining vulnerabilities together, proving access, and demonstrating realistic paths to compromise. It helps answer the question, “What can actually be exploited, how, and with what business impact?”
Mature security programs typically use both approaches. Vulnerability assessments provide broad coverage and hygiene. Penetration testing provides realism, prioritization, and proof.
Key Differences: Vulnerability Assessment vs. Penetration Testing
One of the most effective ways to distinguish scanning from true penetration testing is to ask how findings are reviewed and validated by human testers.
A practical comparison for buyers:
Vulnerability Assessment
- Focus: breadth and coverage
- Output: lists of vulnerabilities with severity ratings
- Best for: asset inventory, hygiene, baseline risk tracking
Penetration Testing
- Focus: depth, exploitability, and impact
- Output: proven exploit paths, evidence, and escalation narratives
- Best for: prioritization, executive decision-making, and control validation (Do controls detect, prevent, contain?)
If a vendor cannot clearly explain how exploitability is proven safely, the engagement may be little more than rebranded scanning.
Types of Penetration Testing Services
Organizations commonly evaluate penetration testing services across the following :
- External network penetration testing
- Internal network penetration testing or assumed-breach testing
- Web application penetration testing
- API penetration testing
- Cloud penetration testing
- Social engineering assessments
- Physical penetration testing
- Wireless penetration testing, often paired with physical testing
- Purple team or adversary simulation exercises
- AI/LLM penetration testing
- Agent penetration testing
- MCP penetration testing
Buyers should prioritize services that align with current risk and change velocity. Selecting a provider solely because they claim to offer every test type can lead to shallow results.
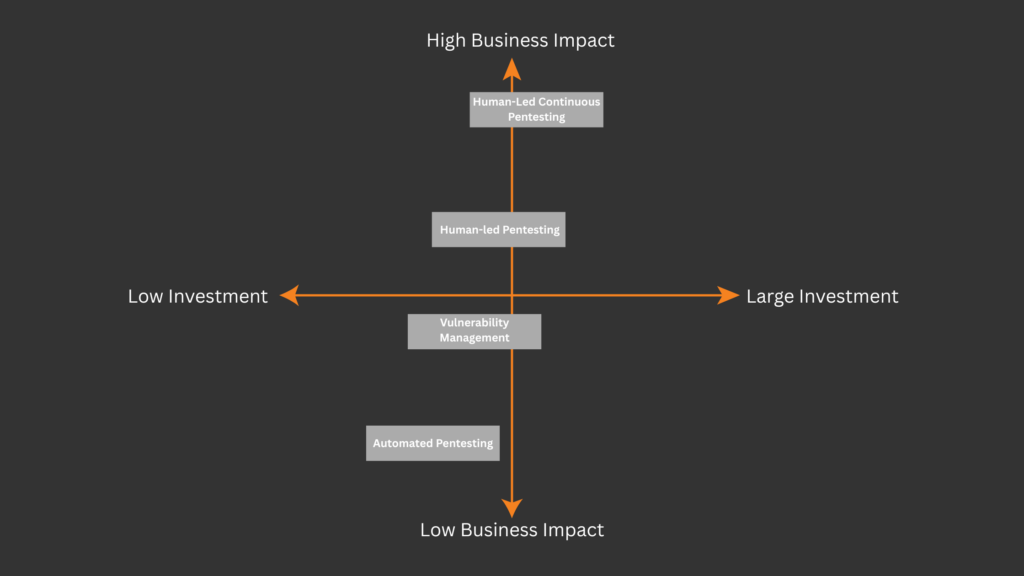
Penetration Testing vs. Continuous Penetration Testing
Many organizations evaluating penetration testing services now encounter the term continuous penetration testing. While the concepts are related, they serve different purposes and deliver value in different ways.
Understanding the distinction is critical when selecting the right approach for your environment.
Traditional (Point-in-Time) Penetration Testing
Traditional penetration testing is a time-boxed engagement designed to assess security at a specific moment.
Typical characteristics include:
- A defined scope and testing window
- Manual testing performed over days or weeks
- A final report delivered at the end of the engagement
- Retesting often scoped separately or scheduled later
Point-in-time penetration tests are effective for:
- Annual risk assessments
- Compliance and audit requirements
- Baseline security evaluations
- Major architectural changes or new application launches
However, these tests represent a snapshot in time. In fast-moving environments, new assets, misconfigurations, or vulnerabilities can emerge shortly after testing concludes.
Continuous Penetration Testing
True Continuous penetration testing (CPT) extends the penetration testing model into a persistent, attacker-simulated service that adapts as environments change.
CPT is not a tool and not scheduled scanning. It is an extension of the security team, combining continuous discovery, automation, and human-led validation to provide ongoing proof of security rather than periodic assurance.
Key characteristics of real continuous penetration testing include:
- Continuous discovery of domains, IPs, cloud assets, and exposed services
- 24/7 automated reconnaissance designed for scale while maintaining a safe cadence
- Human-validated findings that confirm real exploitability, not just exposure
- Rapid validation of new vulnerabilities, often within hours rather than weeks
- Built-in retesting, reporting, and remediation workflows
- Optional purple team and adversary simulation exercises to test detection and response, not just controls
Rather than producing a single report, continuous penetration testing delivers real-time insight into exploitable risk, with findings validated, prioritized, and retested as fixes are applied.
How Continuous Penetration Testing Delivers Different Value
As AI continues to introduce new application patterns and new risks, modern frameworks expect on-going testing, and organizations need security programs that move at the same pace as attackers, combining always-on visibility with reliable verification is recommended for modern environments. Continuous penetration testing shifts the focus from periodic assessment to continuous proof of security.
Compared to traditional testing, CPT helps organizations:
- Reduce exposure by detecting exploitable weaknesses closer to when they appear
- Prioritize real threats using validated, contextual findings instead of raw alerts
- Accelerate remediation by automatically retesting fixes and reducing mean time to remediate
- Support compliance programs such as PCI DSS 4.0 through ongoing control validation
- Maintain confidence between audits rather than only at audit time
What Continuous Penetration Testing Is Not
For buyers, it is important to distinguish true continuous penetration testing from rebranded scanning services.
Continuous penetration testing is not:
- Automated scanning labeled as “continuous”
- Vulnerability management platforms without exploit validation
- penetration testing delivered more frequently without human context
When to Choose Each Approach
Traditional penetration testing is often sufficient when:
- Entirely SaaS, no office, and do not host anything in house
- Environments change slowly
- Testing is driven primarily by compliance
- A baseline assessment is the primary goal
Continuous penetration testing is a strong fit when:
- Any asset exposure online
- Cloud infrastructure and CI/CD pipelines change frequently
- New applications, APIs, or configurations are deployed regularly
- Security teams need faster validation of emerging vulnerabilities
- Leadership wants ongoing assurance, not annual snapshots
Many mature programs use both, starting with a point-in-time penetration test and evolving into continuous penetration testing as complexity and risk increase.
Core Considerations When Selecting a Penetration Testing / Continuous Penetration Testing Firm
Expertise, Experience, and Staffing
Certifications such as OSCP or CISSP can indicate baseline competence, but they do not guarantee engagement quality. Buyers should ask:
- Who will lead the engagement?
- What is the tenure of the staff?
- How recently has the team tested similar environments?
- Will any work be subcontracted?
Methodology and Testing Approach
Ask which frameworks the firm aligns to, such as OWASP, NIST, or PTES. Also ask:
- How manual testing and automation are balanced
- How production safety is ensured?
- How false positives are reduced (they should be eliminated completely) and findings validated?
- Does pentest/CPT include retesting?
Strong testing programs typically automate safe data collection while relying on human-driven playbooks for exploitation and validation.
Reporting Quality and Actionability
Effective reports should include:
- Executive summaries written by practitioners
- Clear exploit narratives and impact descriptions
- Evidence such as screenshots and proof of concept
- Prioritized remediation guidance
Post-Engagement Support
One of the strongest differentiators between vendors is asking the question: Is this firm capable of remediation? If a firm cannot fix the problem, they often will not have the expertise to prioritize real threats, which very often will result into another report of alerts. Buyers should prefer firms that have additional capabilities beyond findings. Inherently, the best results come from advisors that can put the risk in context, validate real exposure, and show your team exactly what to do next.
For Continuous Testing, Communication and Cadence
For continuous testing, buyers should ask:
- How often scans run
- How often do we check have check ins with penetration testers
- How often human testers actively engage
Tools, Techniques, and Technology Stack
Tools should accelerate testing, not replace expertise. Buyers should verify:
- Which activities are automated versus manual
- How findings are validated
- Whether remediation and retesting workflows are supported in a portal
A mature platform often includes risk scoring that elevates high-interest attacker targets, such as exposed SMB services on the internet, rather than presenting flat vulnerability lists.
Legal, Ethical, and Compliance Considerations
Every penetration testing provider should clearly explain:
- Rules of engagement
- Data handling and retention
- Confidentiality agreements
- Permission boundaries
- Safety and stop-test procedures
A lack of clarity in these areas is a serious red flag.
Buyer Checklist: Questions to Ask Penetration Testing Vendors
Scope and Realism
- What attacker scenarios are simulated?
- Is exploit chaining included?
- How is business logic tested?
Team and Staffing
- Who leads the engagement?
- How is consistency ensured across testers?
Safety
- How are outages prevented?
Deliverables
- Can a demo be shared?
- Are reports usable by executives and engineers?
Remediation and Retesting
- Is retesting included?
- What is the retest turnaround time?
Control Validation
- Are pen test replay or purple team exercises offered?
Red Flags and Common Pitfalls
Buyers should be cautious of:
- Guaranteed findings
- Undefined testing staff
- Automated reports
- No retesting process
- Rigid, one-size-fits-all scopes
Claims of continuous testing that rely only on scanning should be examined carefully. Continuous value comes from pairing automation with human validation and rapid response to emerging vulnerabilities.
Cost, Value, and Return on Investment
Penetration testing costs vary based on scope, depth, and seniority. To compare quotes effectively, buyers should ask:
- How senior are the testers?
- How many retest cycles are included?
- How much collaboration time is provided?
Value should be measured in risk reduction and operational clarity, not just price.
Integrating Penetration Testing into a Broader Security Strategy
Penetration testing is most effective when integrated into an ongoing improvement loop:
- Test realistically
- Remediate prioritized risk
- Retest and verify fixes
- Validate controls
- Repeat based on change and threat
Dynamic reporting and continuous validation drive stronger outcomes than annual, static reports.
Frequently Asked Questions About Penetration Testing Firms
Q1: How often should penetration testing be performed?
A1: At least annually for many organizations, and more frequently for high-change environments.
Q2: Is continuous penetration testing right for every organization?
A2: Continuous testing is most valuable where attack surfaces change frequently and rapid validation is needed. It is recommended if your organization:
- Has a large online presence/large external attack surface
- Operates in a high-risk industry like finance, healthcare, or manufacturing
- Cloud + CI/CD environments
- Custom apps and APIs on the internet
- Identity-heavy environment
Q3: What should organizations receive after testing?
A3: A report with evidence, prioritized remediation guidance, and a defined retesting path.
Why Continuous Penetration Testing Is Essential for Modern Organizations
Modern environments change continuously. AI, Cloud deployments, CI/CD pipelines, identity changes, third-party integrations, and new applications all introduce risk. A point-in-time test can provide value, but it can also become outdated quickly.
Continuous Penetration testing is essential because it has all the elements of a strong penetration test:
- Validates real, exploitable risk rather than theoretical exposure
- Demonstrates realistic attack paths and business impact
- Tests security controls such as prevention, detection, logging, and alerting
- Improves remediation quality by showing engineers what truly matters
- Supports compliance, insurance, and customer requirements with evidence
But gives you consistent coverage that is necessary in modern environments.
Conclusion: Choosing the Right Penetration Testing Services
The right penetration testing partner helps organizations reduce real risk by validating exploitability, communicating clearly, supporting remediation, and improving security controls over time.
Penetration testing should not be treated as a compliance checkbox. When evaluated and implemented correctly, it becomes a critical part of an organization’s long-term security strategy.



