Most security programs spend millions on tools and people, then rely on dashboards and assumptions to tell them everything is working. Purple team exercises close that loop.
A purple team exercise is a coordinated test. A pentester runs known attacker techniques against a real environment, while the defenders monitor their controls and their playbooks in real time. The exercise is structured: every technique is mapped to MITRE ATT&CK, every observation is captured against the controls and detections it was supposed to trigger, and every gap is logged for the team to fix. The output isn’t a 200-page report sitting in a SharePoint folder. It’s an evidence-backed answer to three questions a CISO has every quarter:
- Are the security controls we paid for actually working?
- Is the team we hired actually able to detect and respond?
- And what specifically do we need to fix to improve?
1. Control validation: from “configured” to “effective”
Most organizations buy security controls based on what they should do. EDR detects malicious binaries. SIEM correlates suspicious events. Email security blocks phishing. The vendor demo proves it; the procurement decision rests on it; the audit checkbox confirms it; and the managed security service provider will detect it and notify us.
What’s harder to confirm is whether any of that translates into a real signal when a real attacker lands inside your network or systems.
A purple team exercise tests it directly. The pentester executes a credential-dumping technique on a domain-joined host. Your EDR is supposed to detect it. Either it does, or it doesn’t. Either the SOC sees the alert, or they don’t. Either someone responds in fifteen minutes, or no one responds at all. None of those answers are the same as “the dashboard says EDR is healthy.”
In one recent exercise, a credential dumping technique executed successfully across multiple hosts. The EDR generated telemetry, but no alert was triggered, and the SOC never investigated. Within one session, we tuned detection logic, validated alerting, and re-tested the same technique successfully. That gap would not have been discovered through configuration review or dashboards.
The result is a control inventory grounded in evidence rather than configuration. When the next renewal comes around, you know which tools earned their keep and which didn’t. When the auditor asks how you validate effectiveness, you have a documented record of every technique you tested and what your controls did about it. When the executive team asks why an additional EDR module is worth the budget, you can show the specific attacker techniques it would have caught last quarter.
2. Training your SOC the way analysts actually learn
Tabletop exercises are useful. CTFs are useful. Vendor training is useful. However, none of them produce SOC analysts who’ve actually watched a real attack unfold in their own environment, on their own consoles, against the assets they’re paid to protect.
Purple team exercises do all of this, and more. The analyst sees the same alerts, in the same SIEM, on the same shift, against the same network they patrol every day. When the alert fires, they triage it the way they would in production. When they miss something, the pentester explains exactly which technique was running and why their tooling stayed quiet. When they respond well, they get reinforcement and validation that their controls actually work.
This kind of high-context repetition is how analysts move from “I know the runbook” to “I recognize this pattern.” It’s also how new hires ramp up in a fraction of the time, because they’re seeing structured attack scenarios rather than waiting for organic incidents to teach them.
The byproduct, often underappreciated, is morale. SOC analysts spend most of their time on alerts that turn out to be nothing. A purple team engagement is one of the few times they get to see real attacker craft, work it end to end, and leave the day knowing what they caught and what they’d catch next time.
3. Real security improvements, not a list of recommendations
The traditional pentest output is a report. The report names problems. Six months later, half of those problems are still open because no one had the time, the context, or the leverage to fix them.
A purple team exercise is structured to produce remediation, not recommendation. Each technique that wasn’t detected becomes a specific change. This could be a new SIEM rule, a tuning adjustment to an EDR policy, an additional log source feeding the data lake, a refined response playbook. Each of those changes can be re-tested in the next cycle. The improvements compound: the second engagement starts where the first one ends, not from scratch.
That’s what makes purple teaming a security program multiplier rather than a security program audit. The detection engineering team gets a backlog of evidenced, prioritized tuning work. The SOC gets feedback on its own playbooks, and the leadership team gets metrics showing coverage against the techniques most likely to be used against them. Over time, this produces measurable improvements: higher detection rates, faster response times, and increased coverage of relevant attacker techniques.
What a SynerComm Purple Team Engagement Looks Like
A typical SynerComm Purple Team Exercise runs across a defined window (usually 1 day or a half day) with a clear scope. Before the exercise, we work with our clients to select techniques drawn from MITRE ATT&CK and weighted toward threat actors active in the client’s industry. During the exercise, our pentesters execute those techniques on agreed targets while the client’s defenders watch live. Each technique is logged with the exact time it ran, the controls that were expected to detect or prevent it, and the observed outcome. After the exercise, both sides debrief together: what worked, what didn’t, and what the next engagement should test.
The deliverable isn’t a slide deck. It’s a structured record of every technique tested, every control evaluated, every gap identified, and a prioritized remediation plan.
When a purple team exercise pays for itself
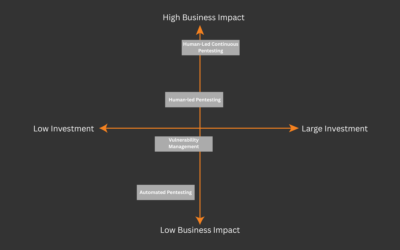
If your organization has any of the following, a purple team exercise will produce returns that show up in the next budget cycle:
- A growing security stack, and a CFO who’s started asking why each line item is necessary
- A SOC team that’s technically capable but under-tested
- A history of audit findings that ask how control effectiveness is validated
- A roadmap that includes detection engineering, threat-informed defense, or zero-trust maturity work
You don’t need to be a Fortune 500. You don’t need a dedicated red team. You need a willingness to find out, in a controlled setting, what your security controls actually do when an attacker shows up.
If you want to see exactly how your controls perform against real attacker techniques, we’ll run a focused exercise and show you the results in a single day.